IAPR/IEEE Winter School on Biometrics
Biometric Data Analysis
2017 | 89 mins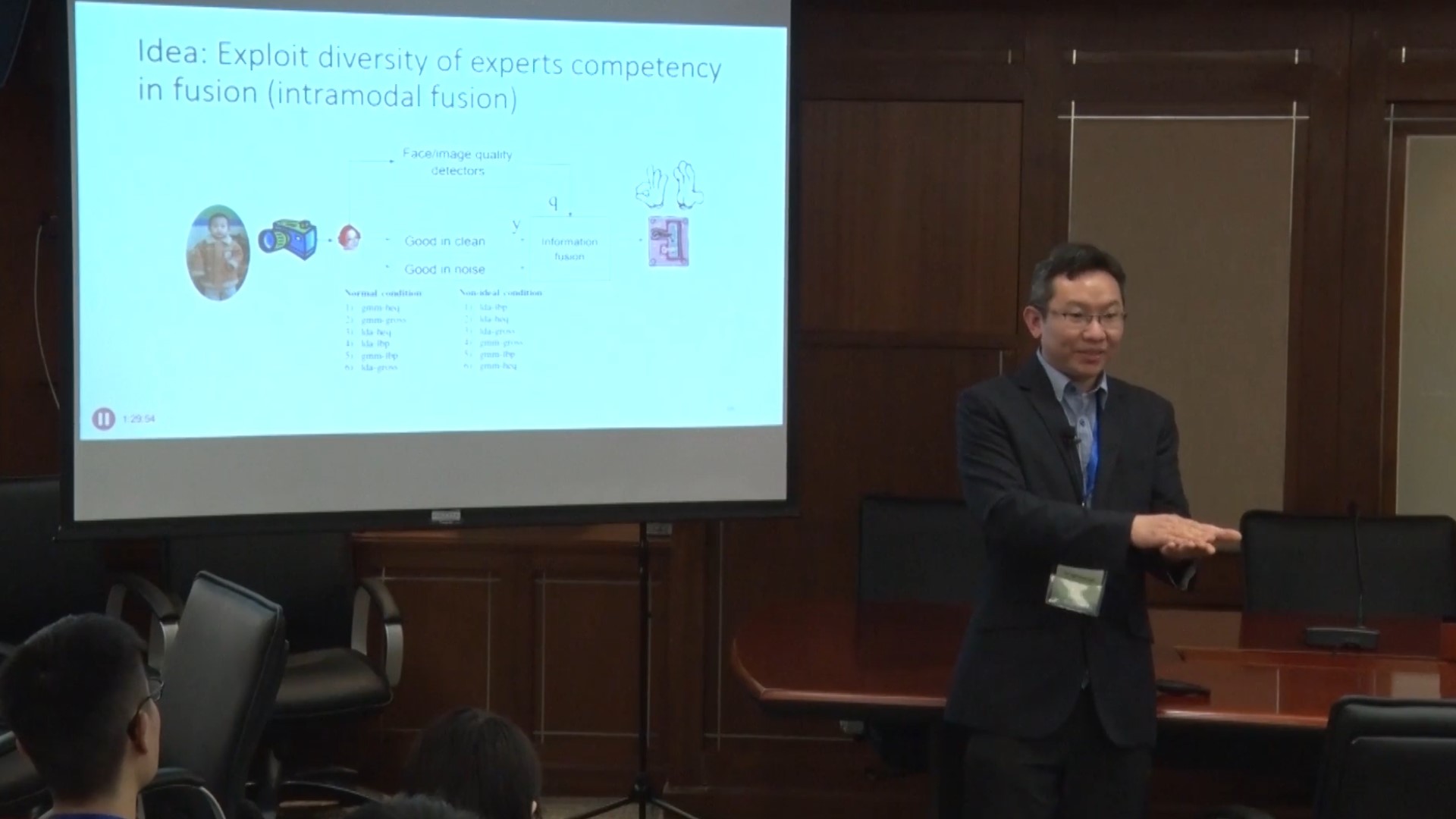
Multimodal Biometrics with Auxiliary Information: Quality, User-specific, Cohort information and beyond
2017 | 97 mins
2D and 3D Face Recognition
2017 | 98 mins
Human Identification via Gait Recognition
2017 | 103 mins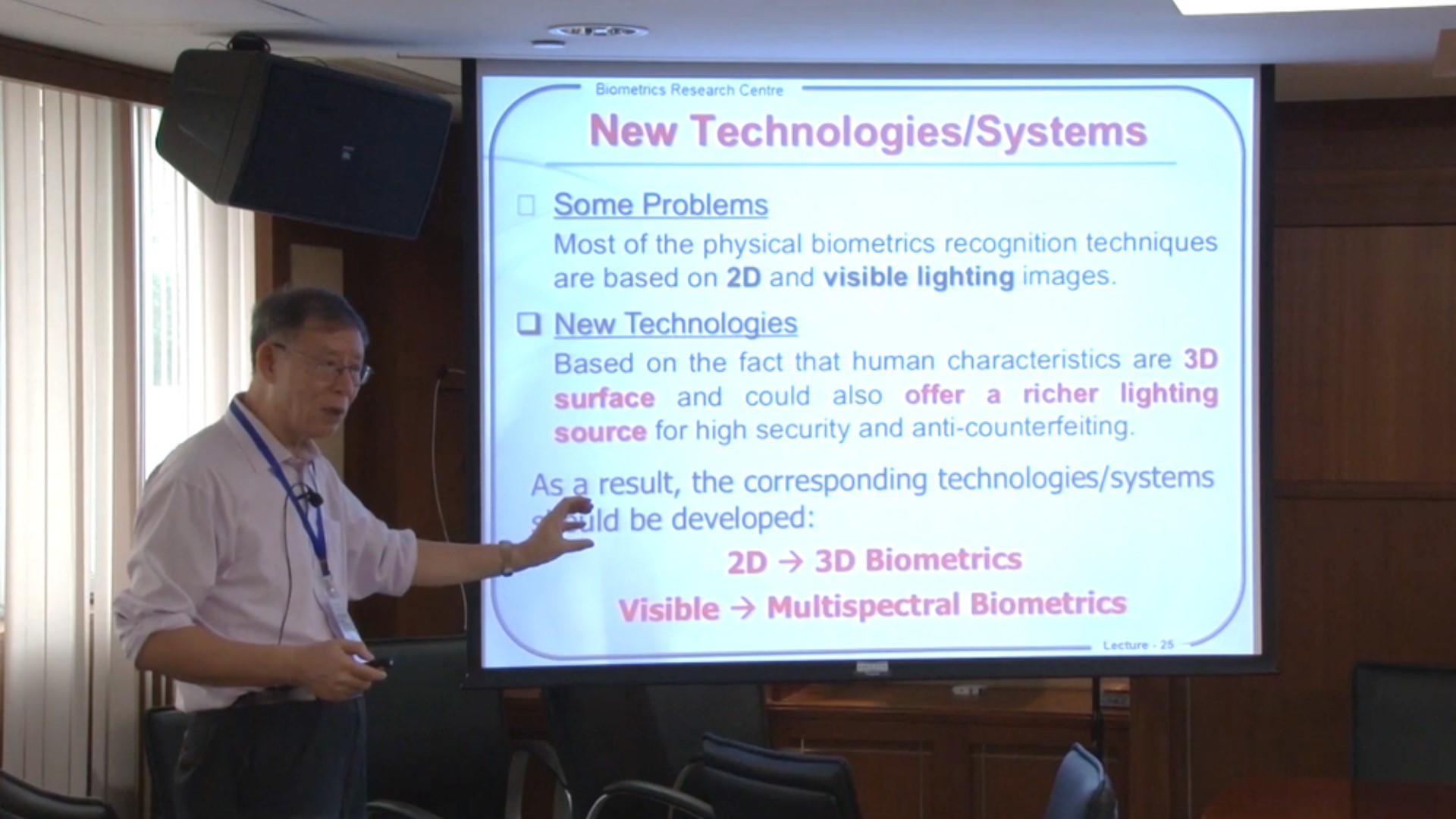
Hand-Based Biometrics
2017 | 91 mins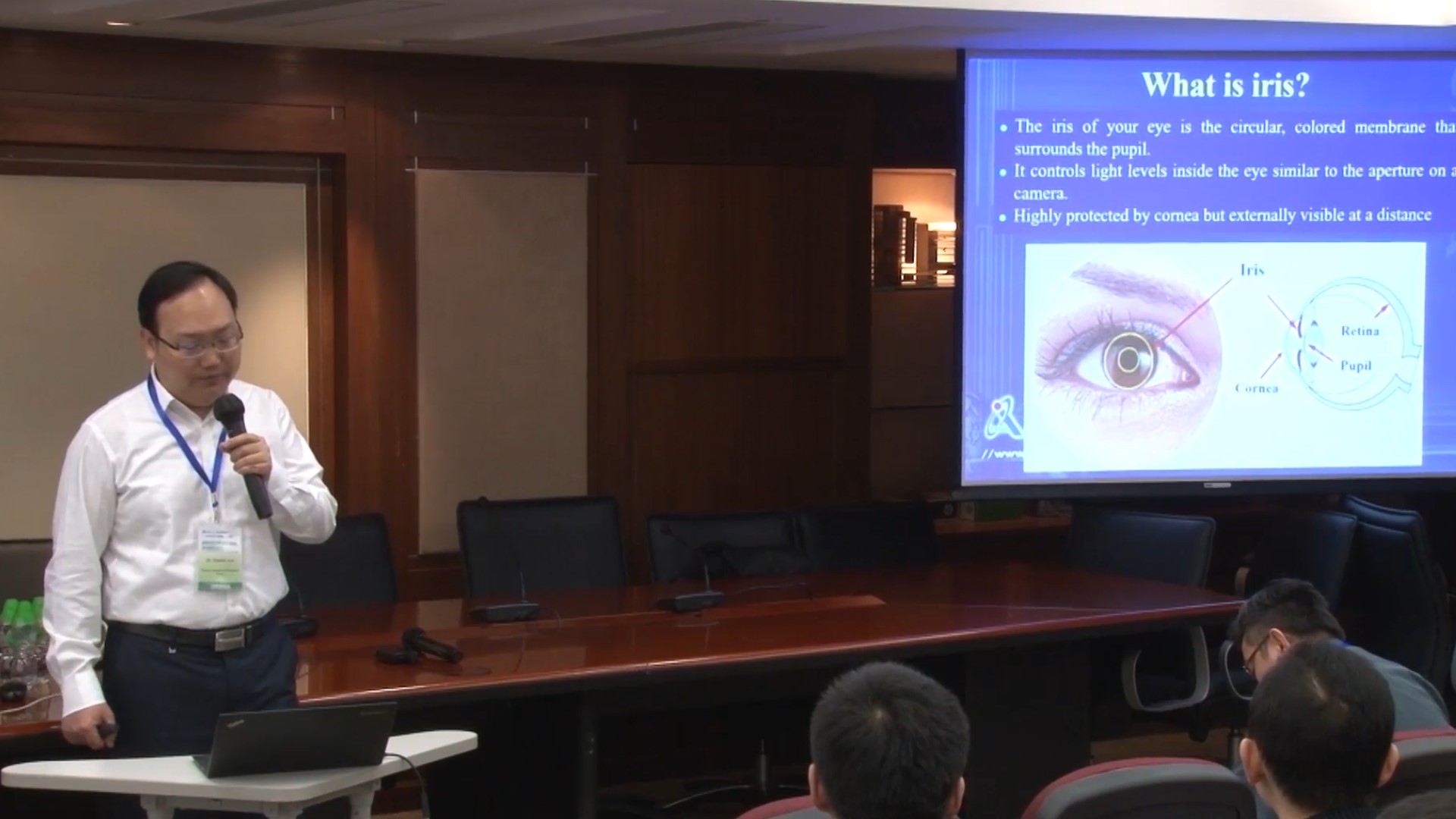
Recent Progress of Iris Recognition
2017 | 91 mins
Mobile Biometrics: Trends and Issues
2017 | 92 mins
Deep Learning in Face Analysis
2017 | 88 mins
Fingerprint Recognition
2017 | 83 mins
Machine Learning for Person Identification
2017 | 90 mins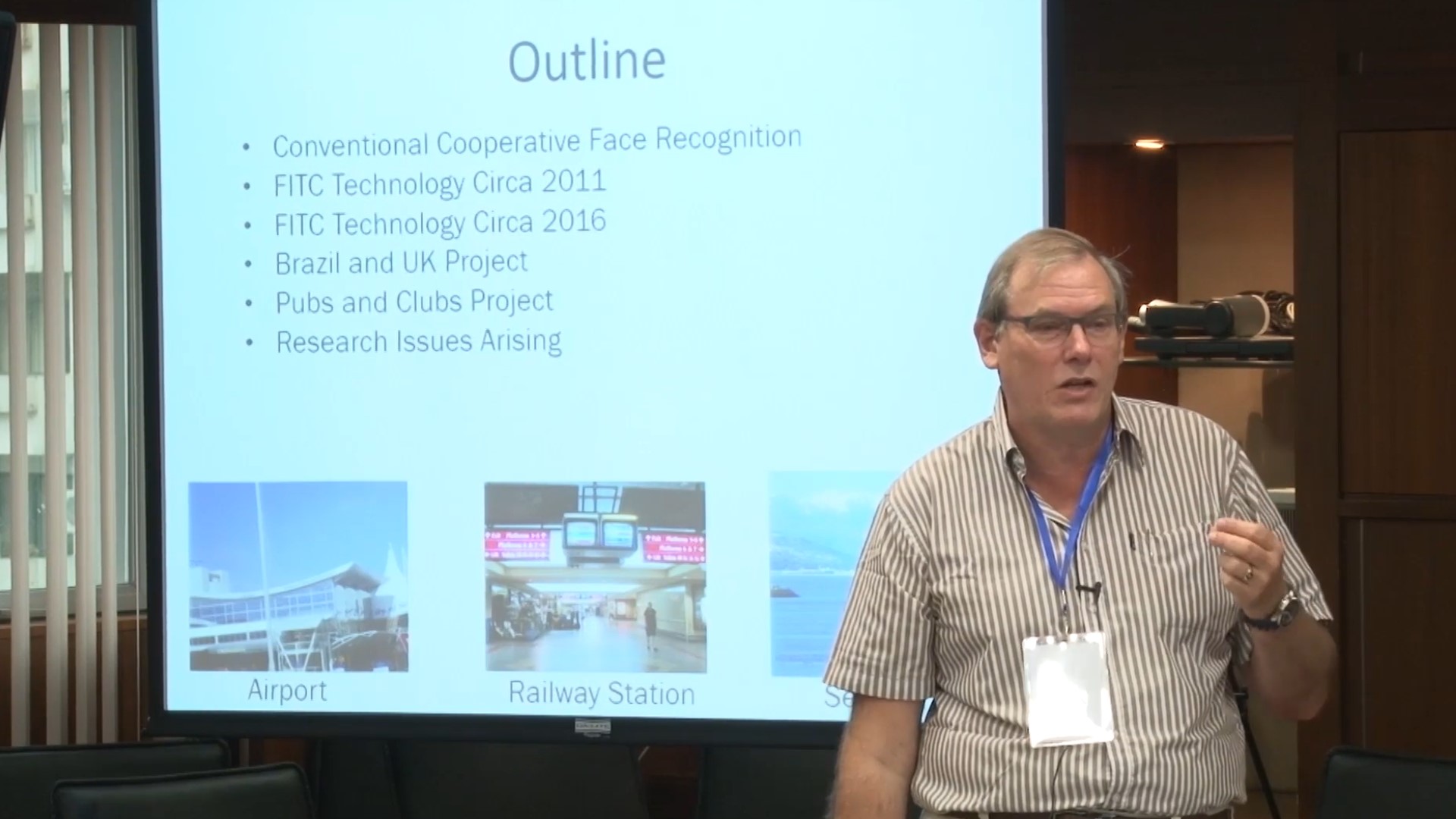
Secure Scalable CCTV, Mobile, and Wearable Video Face Recognition
2017 | 99 mins
Biometric Indexing
2017 | 103 mins
Face Recognition System Security: Template Protection and Anti-spoofing
2017 | 77 mins
Computers and Music
2013 | 22 mins
Will AI Replace Professors?
2025 | 53 mins
Learning to Simplify Sonography during and after the Ultrasound Examination
2025 | 12 mins
Liver Cancer Prediction: From Single Time-Point to Multimodality
2025 | 15 mins
Bridging the Interpretability Gap for Medical AI Models Using a Generative Explanation Approach
2025 | 25 mins
Exploration in Medical AI
2025 | 19 mins
Intelligent Neuromodulation with Edge Computing
2025 | 25 mins
Leveraging 30 Years of Clinical Data and AI Solutions to Advance Healthcare Research, Innovation, and Service in Hong Kong
2025 | 23 mins
AI for Population Health
2025 | 46 mins
Application of AI in Liver Diseases
2025 | 29 mins






